
How to Prevent Cyber Attacks on Businesses
Protect your business from cyber attacks by getting familiar with these common cyber security threats and risk management tips.
Key takeaways:
- Cybersecurity is not optional for businesses. Data breaches cost businesses millions annually, making security essential for all organizations, not just IT teams.
- Human error drives most breaches. Phishing and credential theft are some of the top attack methods.
- Phishing is the most common initial attack vector. Other common threats include business email compromise, ransomware, and exploited vulnerabilities.
- Security awareness is critical. Training employees to spot suspicious communications and conducting regular phishing tests can significantly reduce risk.
- Layered defenses work best. Combine strong processes with technology tools and secure backups for comprehensive protection.
Cybersecurity is a business imperative
For many businesses, cybersecurity was a long afterthought - often left to be a problem for the IT team. However, in recent years, cybercrime has exploded in volume, sophistication and impact, forcing organizations to make security a priority or suffer the consequences. The average cost of a data breach for U.S. businesses is now $4.4 million, according to IBM Security. That number does not include the effect on employee productivity, the company’s reputation or potential lost profits.
The cybersecurity problem increased during the rapid shift to remote and hybrid work environments, which introduced digital infrastructure with a myriad of potential access points for cybercriminals to infiltrate. By using stolen credentials or social engineering trickery, threat actors are often able to compromise security without having advanced technical abilities. Criminals can exploit both vulnerabilities in software and human behavior to hack web applications, export data, launch ransomware attacks and more, not only in your company but in vendors who have access to your systems.
To help your organization manage and prioritize its cybersecurity needs against today’s threat landscape, Fifth Third Bank is presenting a series of articles designed to alert businesses to the latest cyberthreats and provide a detailed guide on how to help protect against them. While the task may seem daunting, the good news is that a strong security foundation can be built even on a limited budget. Arming yourself and your staff with security knowledge is an excellent start.
What are the most common business cyber security threats?
Cybercriminals use a variety of threats to launch attacks against businesses. Often, data breaches happen over a series of security events, making detection that much more difficult. However, if you trace security incidents or breaches back to their root cause, you discover that cybercriminals still heavily rely on a few tried-and-true tactics to gain initial access to business networks.
The most common methods involve manipulating human behavior and emotion through social engineering. Cybercriminals rely on human fallibility for their attacks to work, whether by exploiting behaviors or capitalizing on human error. In fact, 60% of breaches involve the human element, according to the 2025 Verizon Data Breach Investigations Report (DBIR). Despite being one of the oldest cybercriminal techniques, phishing—fraudulent emails that trick users into handing over sensitive information—is still one of the top ways threat actors infiltrate businesses. Phishing is behind nearly 15% of breaches, according to the DBIR.
But phishing is a means to an end, not always the way in. What criminals phish for are credentials, such as employee login information. In fact, credential theft is the leading root cause of data breaches. It’s also the leading result, with cybercriminals stealing additional credentials for their own use or to sell on the black market. Rounding out the top social engineering methods is business email compromise (BEC), which involves threat actors impersonating employees through compromised email accounts.
Additionally, cybercriminals access business networks via exploited vulnerabilities, especially those that are the result of misconfigured cloud components. Whether through phishing, BEC or the use of desktop-sharing software, ransomware attacks are increasingly common against organizations, especially those that not only freeze systems and files but threaten extortion unless a hefty ransom is paid.
See infographic transcript below
Common cyber security threats
Strong cybersecurity for business begins with cyber risk management, including awareness of the most common cyber security threats organizations face today.
1. Phishing
While phishing might be one of the oldest cybercriminal activities, phishing techniques have evolved a great deal over the last couple decades. In IBM’s 2025 Cost of a Data Breach report, phishing replaced stolen credentials as the most common initial vector attackers used to gain access to systems.
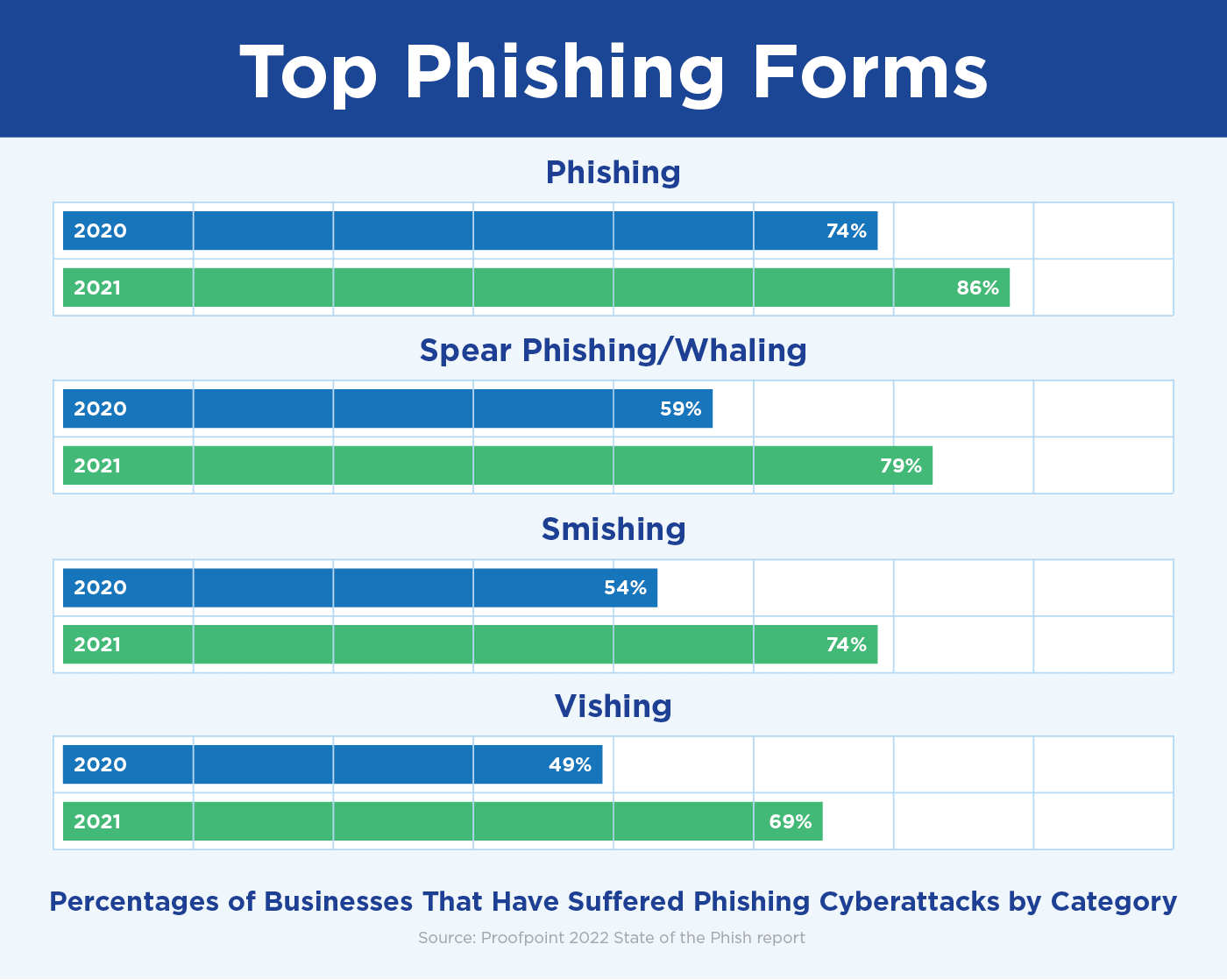
Growing at a faster rate, however, are phishing campaigns that target specific employees or executives, known as spear phishing and whaling. Additionally, vishing attacks, or phishing by voice call. surged 442% in Q2 2024, and this trend continued into 2025. In 2025, the FBI Internet Crime Complaint Center reported receiving 1,573 complaints of smishing, or SMS/text message phishing, in just one month. That’s number nearly matching the total for the previous 14 months combined.
One of the most popular and successful phishing methods against businesses is to send fraudulent emails posing as a vendor, partner or service used by the organization. Pretending to be one of those accounts needing updated profile information can trick staff members into entering their credentials into a malicious website.
Phishing campaigns can do more than collect credentials, however. Employees that open attachments or click on embedded links could be inadvertently launching malicious software or malware, such as downloaders that install on systems and wait for instructions or worms that spread laterally before dropping ransomware on servers and endpoints.
2. Business email compromise (BEC)
63% of respondents from the 2025 AFP® Payments Fraud and Control Survey cite business email compromise (BEC) as the number one avenue for fraud attempts.
BEC is a major threat vector for cybercriminals because employees use email as a main communication method and are trained to trust messages from their coworkers, especially their superiors.
In a BEC scenario, criminals send an email that appears to come from a known source making a legitimate request, such as a CEO asking her assistant to purchase dozens of gift cards as employee rewards or a vendor sending an urgent invoice with an updated mailing address. When cybercriminals can compromise or copy a business email account, a process known as spoofing, they can easily dupe employees into committing fraud without realizing their mistake.
3. Credential theft
Credential theft is one of the leading causes of data breaches, according to the IBM Cost of a Data Breach 2025 report. In addition, stolen or compromised credentials took an average of 246 days to resolve and cost businesses an average of $4.67 million globally.
Credentials can be obtained by cybercriminals in several ways, from phishing emails to sales on the black market—even simply found in unsecured, cloud-facing databases. In addition, threat actors steal credentials from organizations in data breaches, either to access web applications and privileged accounts or to sell to the highest bidder. As our reliance on internet-facing software grows, so too will cybercriminal attempt to abuse our digital identities for profit.
4. Ransomware
According to the 2025 Verizon DBIR, ransomware increased by 37% from last year’s report—a jump from 32% to 44% of breaches. In addition to volume and frequency, ransomware attacks have also increased in complexity and impact. And threat actors rarely settle for a negotiated insurance payout.
Ransomware attacks against businesses today are rarely solo events. Instead, cybercriminals typically gain access to networks through desktop-sharing software, unauthorized use of credentials, malware dropped in phishing emails or exploited vulnerabilities. They then deploy ransomware to monetize their access. However, locking systems and encrypting files is no longer where a ransomware attack ends. Most now include threats of extortion, with criminals publishing sensitive data on public-facing websites unless more money is delivered.
5. Exploited vulnerabilities
About 20% of breaches were caused by exploited vulnerabilities, according to the 2025 Verizon DBIR. Some of these are the result of not updating software and operating systems, as well as zero-day exploits, which are vulnerabilities that are discovered by enterprising cybercriminals before patches can be created and deployed.
Another possible cause is IT staff accidentally misconfiguring cloud components like firewalls, APIs, cloud email servers and web applications. This creates vulnerabilities that serve as network on-ramps for bad actors. If buckets are created without proper access control lists (ACLs) defining who has access and at what level, they can "leak" data onto the open internet. And because buckets often house sensitive information, this data can later be used for attack.
How can you protect your business from cyber attacks?
For a long time, it was enough for businesses to purchase technology, such as firewalls and antivirus protection to stop most cyberattacks. However, today we all need to do more. While technology can thwart many cyberthreats, the most important factor in mounting a full defense of your organization is the security awareness of its people. By teaching employees how to identify and avoid digital threats, you can change the human behavior cybercriminals rely on for their schemes to work. By implementing smart processes and technologies, you can protect the health of your systems, too.
Keeping cyber defense strategies front-of-mind is crucial for ongoing protection. Here are a few cybersecurity tips your organization can take to protect against the top cyberthreats today:
Protect with security awareness
Cyberthreats: Social engineering, phishing/smishing/vishing, BEC
Train employees to review all communications with skepticism, including those from coworkers. Be aware of the following:
- Urgent language requiring action immediately
- Strange payment requests outside of normal processes
- Requests to update profile information via hyperlink
- Emails from unknown senders with attachments
Conducting regular phishing tests and collecting metrics helps to determine if the training is working. It’s also helpful to offer seminars on the latest cyberthreats and tips to avoid them each quarter.
Protect through process
Cyberthreats: Exploited vulnerabilities, credential theft
- Immediately update all operating systems and software when updates are released.
- Set updates to automatic, if available.
- Configure cloud buckets to "private" and include ACLs to determine access privileges.
- Implement strong password requirements, including at least 10 characters with numbers, symbols and upper- and lower-case letters.
Protect with technology
Cyberthreats: Credential theft, ransomware
Consider using a single sign-on service (SSO) for all web applications that is protected with multi factor authentication (MFA). MFA adds an extra layer of security by requiring two or more forms of verification to access platforms, including:
- Something the user knows, such as a username or password
- Something the user has, such as a security token or a cell phone
- Something the user is, such as a fingerprint or face ID
Additionally, layering security software with anti-malware and anti-ransomware programs can detect, respond to and remediate cyberthreats. Implementing automatic backups that are stored in a secure cloud platform (or on a server segmented from others) is another best practice.
Cybersecurity is no longer just a problem for the IT helpdesk. All employees, partners and third parties of an organization need to be vigilant to protect against today’s threats. The cybersecurity expertise provided here and in future articles in this series will help you gain the skills to protect customer and proprietary data, devices, networks and even the health and finances of your business. By increasing your security awareness, you make your organization and its digital infrastructure a safer place for all employees.
Learn more about cybersecurity best practices for your business finances.