
The Costly Connection Between Hackers and Healthcare
Healthcare’s race to innovate has never been more intense – and neither has the onslaught of cybercrime as a result. What can the industry do?
In late 2020, an American hospital network discovered that cybercriminals had breached its system. The IT staff acted quickly, shutting down the network’s health records system, but not before hackers paralyzed its nerve center by encrypting information on 1,300 servers, disabling communication systems, and leaving staff without access to email and patient records. In the weeks until services were fully restored, reports show that the network furloughed more than 300 workers and lost about $1.5 million per day.
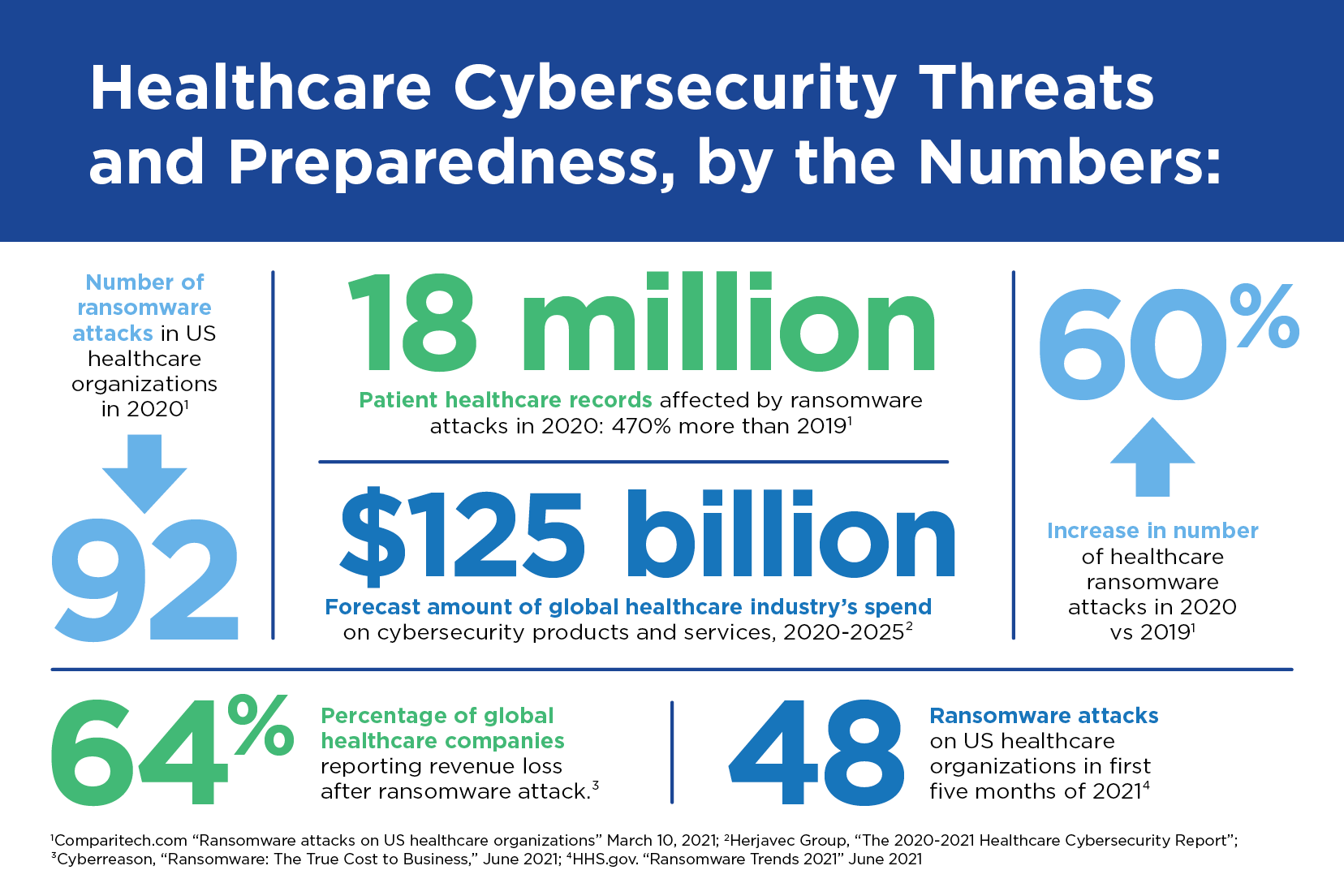
While this was a particularly devastating incident, it demonstrates a critical problem the industry faces today: The more it transforms digitally and embraces the latest medical technologies, the greater the number of attack points for cybercriminals. The rise of COVID-19 and social distancing mandates accelerated the telemedicine trend, as well as the use of Internet of Medical Things (IoMT) devices used to treat patients remotely. Reports show that in 2020 cybercriminals took advantage of an industry grappling with a pandemic to launch attacks on 560 U.S. healthcare facilities and to extort ransoms for stolen patient data. In the past six months, nearly half of all U.S. hospitals have had to disconnect from their networks due to ransomware, and average ransom payments are reported to exceed $130,000.
"These devices are making care more streamlined, cost-effective, and easier for patients to be treated from their homes," says Tom Scarborough, Senior Director of Extended Security Programs at Fifth Third Bank. "But almost every device becomes a potential point of intrusion into the system that uses that device." Even before the pandemic, a 2018 report estimated more than 500,000 IoMT different types of smart devices were in the medical market, and forecasts put the global market valuation for this technology at $158.1 billion by 2022.
Healthcare organizations are prime targets for cybercrime given the vast amounts of highly sensitive patient data they hold, the wide array of digital hardware they utilize, and the need for that information to be accessible to a large number of people. Hackers have long considered healthcare facilities "soft targets" since they generally lag behind other industries in cyber resilience and are not held to the same strict data regulations as, say, financial institutions. "What healthcare companies can take comfort in, however, is that there is plenty they can do to minimize the impact of cyberattacks," says Scarborough. "It takes the persistent practice of basic cyber hygiene, including strong protocols to follow in the event of an attack."
The Cyber Defense Triad: Technology, Processes, and People
Bolstering healthcare cybersecurity requires more than just technical solutions. Organizations need to evaluate day-to-day processes in terms of their security risk exposure and also turn every employee into a front line of defense, by persistently educating, training, and testing their ability to spot an attack attempt.
Here are a few steps that can mitigate a health organization’s cyber risk:
- Install a business continuity/disaster recovery plan and persistently put it to the test. A quality response plan is paramount for every organization, not just to contain a cybersecurity breach, but for any IT outage. "Companies have contingency plans for power failures and natural disasters; cyberattacks should be added to the list," says Scarborough. The Ponemon Institute’s 2021 "Cost of Data Breach Report" puts the average cost of a data breach at $4.24 million, with healthcare being the costliest ($9.23 million). The purpose of planning for disasters is to reduce the time it takes to recover and to mitigate the extent of damage. There are many business continuity plan (BCP) and IT disaster recovery plan (DRP) templates and software applications available in the marketplace, but here are the basic elements of a BCP or DRP:
- Back up data and send it to physical off-site locations. "One of the most important components of a DRP is having off-site backups, and making sure those backups are completely isolated from your main network is key, so they aren’t encrypted as well," says Scarborough.
- Test your disaster recovery plan. "We also cannot stress enough the importance of regularly carrying out tests," says Scarborough. "Testing will expose the weak links in your plan ahead of an attack and help to ensure your employees act like clockwork when it comes to following protocols."
- Maintain updated contact information. Key staff members in particular need to be contactable wherever they are when a breach occurs.
- Update your plan. Businesses and technologies are constantly changing, so it’s important to continually revisit your plan.
- Develop an incident response plan. Healthcare organizations should treat cybercrime as an eventuality, not a possibility. The best way to bake it into business continuity processes is to incorporate an incident response plan into a disaster recovery plan.
- The key difference between the two is that incident response refers to the scope of actions to be taken during an attack to protect sensitive data, while disaster recovery planning ensures you have the steps in place to bring your business back to an operational state after an incident occurs. The plans work together to minimize the impact of an unexpected event, provide a recovery roadmap, and get the organization back to normal as fast as possible.
- The National Institute of Standards and Technology (NIST) provides incident response plan best practices in its Computer Security Incident Handling Guide. The key elements include:
- An incident response team. IT should lead the incident response effort. Roles and responsibilities need to be clear and include IT leads with strong executive support and interdepartmental participation. The team’s goal is to coordinate and activate team members across lines of business to investigate, analyze, and minimize the impact of the attack. AT&T gives a thorough outline of what each team member should do.
- Testing the plan regularly. "Testing is critical," says Scarborough, "because of the nature of the beast: If technology is forever changing, then there’s the potential for the types of attacks to change as well. That requires response plans to be consistently tested and updated."
Organizations don’t have to reinvent the wheel. The cybersecurity industry is a collaborative one that provides a bounty of resources. The SANS Institute, for instance, provides a variety of incident handling forms, to ensure documentation of how a plan is carried out during a live or test-run attack. And TechTarget provides a completely editable and downloadable plan template.
- Demand cybersecurity best practices in vendor contracts. A 2020 study found that the average organization engages more than 1,400 third-party vendors, and that about 70% of these companies don’t monitor the vendors’ cyber defense preparedness. Many cyber incidents begin when criminals exploit a weakness within a third party’s systems and use that company as a jump-off point for campaigns against their intended targets. But just as healthcare organizations may have to observe HIPAA regulations in their engagements with outside parties, they can also use contracts to ensure key partners are deploying strong cybersecurity protocols in their own networks.
- Demand safer code in medical devices. IT leaders at major hospitals can become more proactive about ensuring developers’ IoMT devices are coded from the get-go to be more resilient to attack. Security features of these devices are often add-ons, rather than built-in, which often makes them easier for hackers to access an application’s database. From there, data can be stolen and the behavior of the application itself can be compromised.
- Implement effective tools. Email filtering systems, advanced detection and response solutions, web proxies, mobile device management, VPNs, and other technology can help health IT professionals protect their networks, spot anomalous behavior, and remediate breaches.
- Regularly apply patches and updates to software and connected devices. All organizations depend on software companies, who regularly update their products with security patches. It’s the organization’s responsibility to stay current and effectively mitigate vulnerabilities.
- Review access management protocols. A health organization’s most critical data can be protected through stricter controls around who can access it, and when. By implementing controls that provide file and account access only to those who need it, the company can better protect against encryption or exfiltration of data.
- Outline and champion security best practices. Organizations should leverage protocols such as two-factor authentication and zero-trust security framework, which require continuous authentication and authorization of users in an organization’s most critical systems. All employees should be encouraged to follow strong password management, check the security of their remotely connected devices, and develop a critical approach to any unsolicited communication.
- Create a culture that treats cybersecurity as a core business value and objective. "Employees can either be an asset or a weakness to the organization’s security," says Scarborough. "With effective training, messaging, and encouragement, a company can empower their employees and help them to prioritize awareness and best practices."
- Increase cybersecurity spend. Evidence suggests the healthcare industry is underinvested in its technology and employees: By one estimate, hospitals invest about 5% of their IT budgets in cybersecurity. Another study states that just 24 % of healthcare workers reported receiving any formal cybersecurity awareness training, although many had requested it.
As digital transformations continue to change the healthcare industry’s operations and systems, criminals will create new tactics for breaching companies’ defenses. But organizations that make cybersecurity the business of every employee can distinguish themselves and earn trust from patients, partners and the public. For additional information, contact your Relationship Manager or Treasury Management Officer or Find a Banker to learn more.